Learning Nessus
Welcome back to my blog. This is a write-up on the Nessus Pluralsight course.
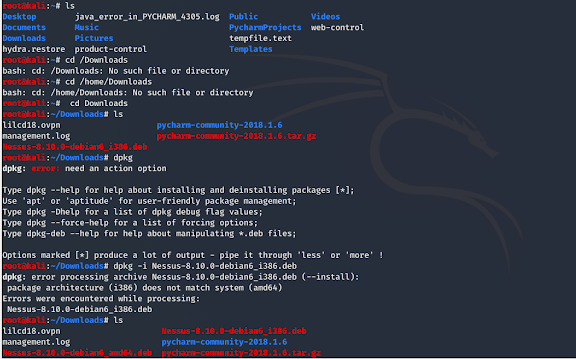
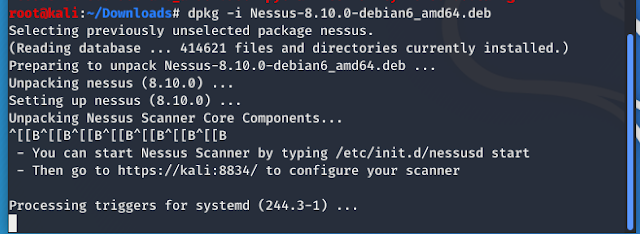
First, I download Nessus for Kali Linux. Then I got an activation code sent to my email address. I used the dpkg -i command to install Nessus. When you get to the web interface create your Nessus account and then enter your activation code. When you install Nessus make sure you download the correct version. I am using the Nessus essentials version for this blog post.
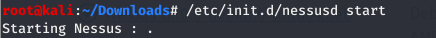
This is the command to start the Nessus service.
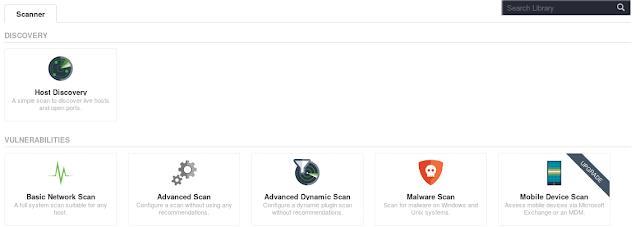
This is the interface to create a new scan. Nessus usually runs on https://localhost:8843 by default. You need to add Nessus as a security exception.
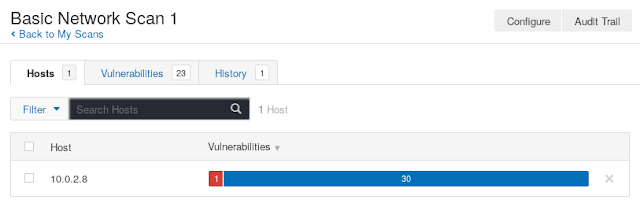
I set up a basic network scan of one of my Vulnhub machines. This is the result of the scan. Red or critical vulnerabilities are very important to investigate.
One critical vulnerability was found. Critical vulnerabilities should be fixed immediately.The risk factor is critical.
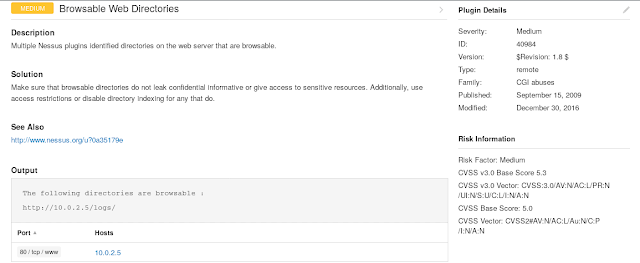
This scan even gives you more information on how to exploit the vulnerability. Security analysts could test the exploit in a controlled environment to verify the vulnerability scan's accuracy.
I also set up a web application vulnerability scan. This type of scan can give you more detailed results into vulnerabilities specifically for a web server. I was able to find an open directory in this vulnerable web application. Open directories are a big vulnerability for web applications because attackers can use open directories for enumeration or exploitation of your web server.
Overall I feel like Nessus is a great vulnerability scanner if you can afford the price. The free essentials version is perfect for testing purposes. A combination of OpenVas and Nmap is a great free alternative.
Thanks for visiting my blog!
Please leave a donation with the link below if you would like to support the blog.